国产信创要求+安全事故频发,加速各行各业替换 AD
国产信创要求趋严
需要更合规的迁移方案
需要更合规的迁移方案
AD 攻击日益频繁
需要更灵活的防范策略
需要更灵活的防范策略

为什么选择 Authing 替代 AD 目录?
使用 AD,面临传统软件带来的诸多挑战
多种认证协议未支持
AD 仅支持 LDAP、Kerberos 协议,企业若想与更多业务系统集成,需付出大量的研发成本。
多种身份场景难满足
AD 主要用于「域内的权限控制」,单点登录、数据同步、账号管理等围绕身份管理的能力,较为薄弱。
耦合度高,故障易发生
企业依赖 AD 为所有业务系统的登录核心服务器,容易导致 AD 的任何重启、补丁更新,影响其他业务系统。
扩展性低,系统难升级
AD 作为有 20 年历史的系统,API 和扩展能力较缺乏,IT 运维、Bug 修复等成本负担大。
使用 Authing,构建国产信创的身份管理体系
集成多种协议和应用,减少研发成本
Authing 支持 LDAP、OIDC、OAuth2.0、SAML、CAS 等多种认证协议,预集成了 2000+ 常见应用,方便企业快速接入。
贴合企业多元的身份管理场景
使用 Authing 作为统一身份认证与管理系统,集成 AD 域控,能同时兼顾单点登录、账号生命周期管理、权限管理、多因素身份认证等能力,提供企业更完善的解决方案。
轻松解耦 AD,减少 AD 的维护风险
以 Authing 作为主要的身份管理平台,将身份信息与设备信息剥离,能减少 AD 域事故的发生,减少 IT 的工作负担。
基于 PaaS 能力,支撑企业未来 5-10 年的业务扩张
Authing提供丰富的 API/SDK 和登录组件,基于云原生、Serverless 能力,能灵活配合业务需求、快速选代升级,减少 IT 运维的工作量。
信创先锋企业都选择 Authing 实现替代方案
长鑫存储

四维图新

万科集团
平稳迁移 AD 目录 100%
通过 Authing 身份自动化和元数据能力,将 AD 目录完整映射至 Authing,无需重新构建目录。
先进制造行业
国内领先的半导体 IDM 企业,目前已建成第一座 12 英寸晶圆厂并投产。
使用产品
AD 迁移
身份认证
统一账号管理
Authing 帮助我们无痛解耦 AD 设备管理和人员账号管理,让 AD 管设备、Authing 管身份,大幅减少维护风险,实现统一的身份认证底座。
数据迁移 0 负担
终端用户无感知
Authing 已帮助多家大型企业进行无痛迁移,积累丰富的实践经验
完整映射身份字段和框架,无需重新构建目录
快速打通多个应用数据,无需改造老旧系统
自定义数据库连接方案,保障数据迁移的安全性
选择高安全、高性能、高生产力的身份产品
- 高安全
- 数据存储使用 AES-256 算法加密;通过 SSL/TLS 协议加密传输;使用 KMS 管理密钥,密钥定期轮换。
- 7x24 小时的安全应急响应;两地三中心备份,保证灾难时快速恢复。
- ISO、等保三级、数据保护条例等多项认证。
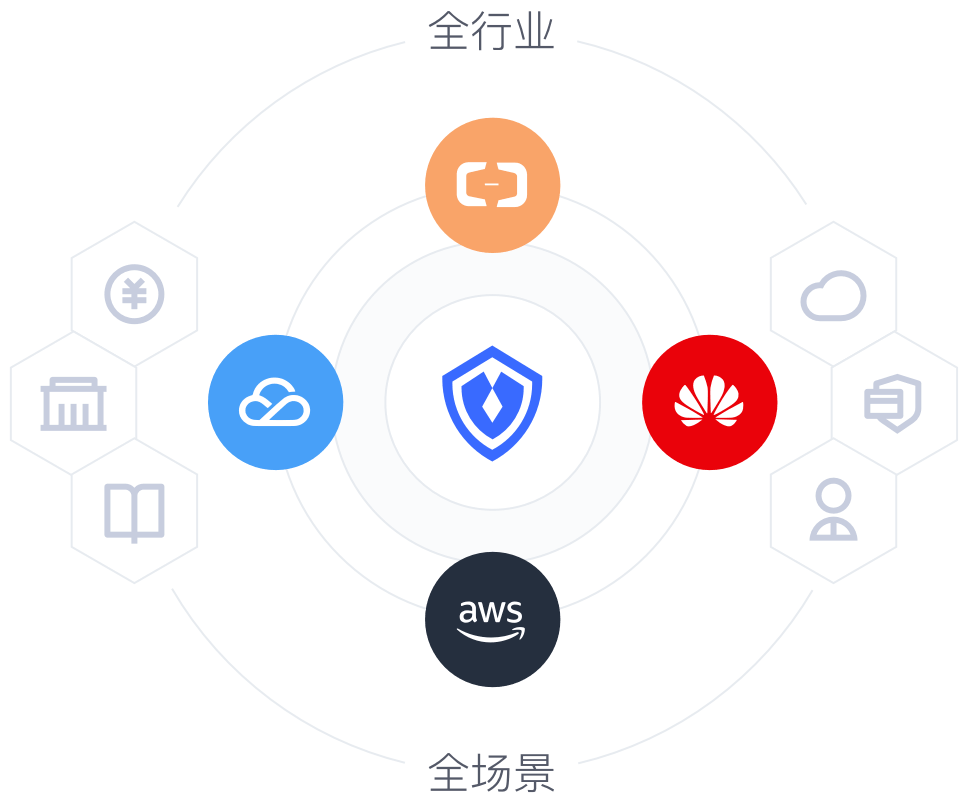
- 高性能
- 云原生:采用 Kubernetes 容器化技术,支持分钟级别弹性扩容,可支持亿级别用户认证访问场景。
- 云中立:兼容用户的云环境,不被原有的云厂商捆绑。
- 高生产力
- 开发者友好:提供丰富登录、认证、授权 API/SDK,降低研发成本。
- 快速集成 2000+ 主流应用,简单、高效的建立身份中台。
快速集成 五分钟实现
单点登录、认证授权、权限管理等功能